
What Are the Best AI Tools for Enhancing UK Customer Service?
In the fast-paced world of customer service, businesses in the UK are constantly seeking innovative ways to improve their interactions with customers. Today, artificial intelligence[…]

How to develop a comprehensive cybersecurity framework for UK’s fintech startups?
In today’s digital era, fintech companies have revolutionized the financial landscape in the UK by leveraging cutting-edge technology to offer innovative financial services. However, the[…]

What are the best practices for securing AI-powered customer service platforms?
In today’s rapidly evolving digital landscape, AI-powered customer service platforms have become central to enhancing customer experience and satisfaction. These systems leverage artificial intelligence (AI),[…]
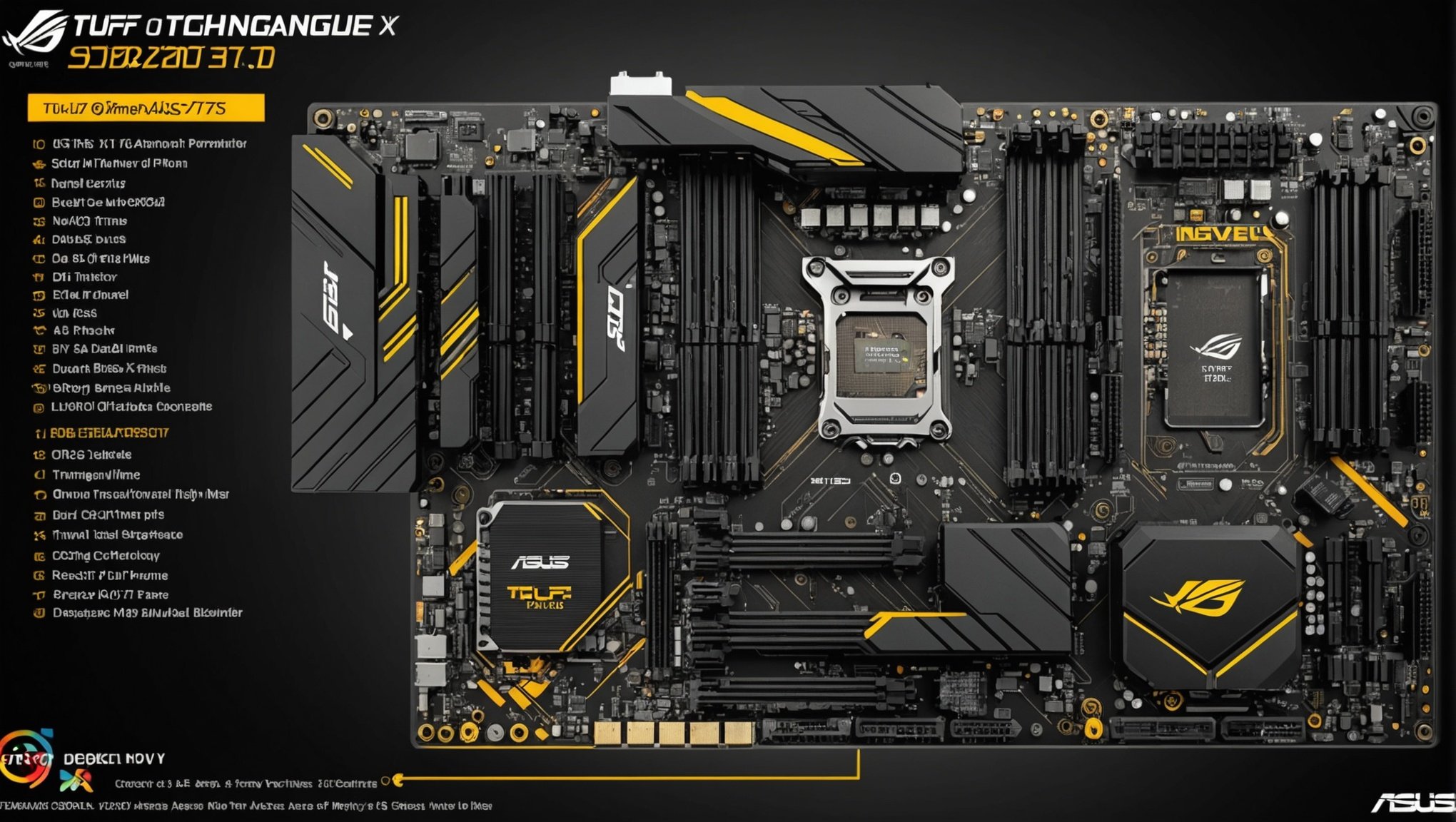
What are the optimal settings for configuring an ASUS TUF Gaming X570-Plus for high-speed data transfer with NVMe SSDs?
When it comes to high-performance gaming and professional computing, the ASUS TUF Gaming X570-Plus stands out as a powerhouse motherboard. Designed to work seamlessly with[…]

How can UK fintech startups ensure compliance with evolving international financial regulations?
The fintech industry is booming, offering innovative financial services that are reshaping how people interact with money. However, with great innovation comes the significant challenge[…]
How can AI-driven tools be used to enhance remote patient monitoring in healthcare?
Healthcare has always been at the forefront of applying technology to improve patient outcomes. Today, the most exciting development is the fusion of artificial intelligence[…]

How can you configure a Lenovo ThinkPad P52 for efficient machine learning model training?
In today’s rapidly advancing tech landscape, machine learning (ML) has emerged as a cornerstone of innovation. From predictive analytics to intelligent automation, ML models are[…]

What are the best practices for implementing email authentication protocols like SPF, DKIM, and DMARC?
In the digital age, email communication has taken center stage in business and personal exchanges. However, accompanying this surge is the rise of nefarious activities[…]

How to implement a zero-trust security model for cloud-native applications?
In an era where cyber threats are increasingly sophisticated, traditional security measures no longer suffice. Companies are steadily migrating to cloud infrastructure, necessitating a robust[…]

How can you use CloudFormation StackSets for managing multiple AWS accounts?
Amazon Web Services (AWS) provides a robust platform for managing virtual services and resources. However, as you scale up, you may find yourself dealing with[…]